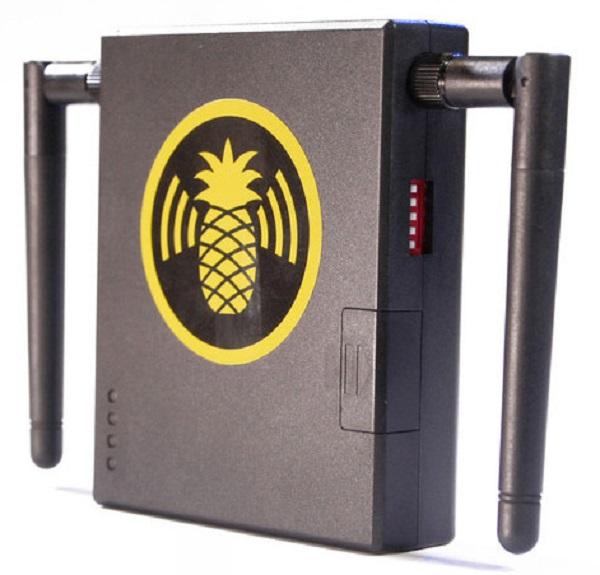
Wi-Fi Pineapple: A Rotten Piece of Fruit
The Pineapple has five different lure and attack modes: Reconnaissance, Auto Harvest, Dogma, Beacon Response, and Karma. Reconnaissance lets the user visualize the Wi-Fi landscape to target entire networks or just specific individuals. Auto Harvest collects probe requests and beacons sent out by devices looking for a trusted Wi-Fi connections and then stores them for rebroadcasting. Dogma attracts specific targets or all nearby devices by emitting thousands of beacons. Beacon Response mimics known and trusted networks with automatic targeted beacons. And Karma captures clients no matter what network they seek. Scary stuff, especially when you read Hak5’s description of what man-in-middle attacks permit.
“By thoroughly mimicking Preferred Networks, this advanced Rogue Access Point suite attracts modern smart devices into connecting to the WiFi Pineapple. Capable of impersonating public and secured WiFi access points, with its device specific precision, PineAP provides the penetration tester with targeted client acquisition capabilities. In this scenario the attacker can monitor all network traffic flowing between an Internet gateway and the connected clients as well as manipulate this data in transit such as through captive portals, DNS spoofing, IP redirection and even the substitution of executables in transit.”
To find out how to protect yourself from being Pineapple’d, I reached out to Pakedge, manufacturer or enterprise grade networking components preferred by many custom installers. Here are their five suggestions.
1) Limit your WiFi use. Obviously this is not always possible, but the most secure device is a device not connected to a wireless network. If possible use a hard-wired, Ethernet connection when managing sensitive data like financial or personal information. Or use a cellular connection. Beyond that, those who are still concerned about WiFi hacking should also get into the habit of turning off the WiFi when it’s not in use - and pay attention to suggestions 2-5.
2) Remove any stored, “trusted” networks on your device that are set to “automatically connect.” This will keep your computer from broadcasting these names and giving the Pineapple nothing to mimic. This will require you to manually enter in your password and manually connect each time, but it will prevent you from having your credentials “spoofed” and then jumping onto a rogue network. If that is too extreme, go through your wireless connections settings periodically and delete the networks that you are unfamiliar with or that you don’t use regularly.
3) Make sure all of your firmware and patches are up-to-date and only run updates when you are connected to a known, secured network.
4) Don’t connect to any open networks such as “Free WiFi” when out and about. In fact, you shouldn’t connect to any network that isn’t running the latest WPA2 encryption as the Pineapple can’t impersonate networks If you need to connect when out and about, connect through a virtual private network (VPN) as the data will pass through but be encrypted. If you are connected to a free network, don’t access any sensitive information such as banking info or visit any sites that require you to type in a user name and password.
5) Encrypt your home’s network with a robust password using WPA2 and don’t give out the password to anyone. Instead create a secured “guest network” for guests to access the Internet only, but not have access to your data.
Darren Kitchen, one of the co-creators of the Pineapple, offers this additional suggestion to avoid being sucked in by his product. “The fundamental premise of a Wi-Fi Pineapple's attack is simply lying to a nearby laptop, tablet or smartphone -- saying "Yes, I am the network you're looking for". I add a network on all of my devices called ‘Pineapple Alert’ - so my phone for example is constantly looking for it. If ‘Pineapple Alert’ shows up in my list of nearby access points I'll know there's a Wi-Fi Pineapple nearby. While there are workarounds to mitigate the attack, such as disabling the ‘automatically connect to remembered access points’ feature in most operating systems, I simply bypass Wi-Fi completely when out and about using a 3G USB modem instead – but then again I'm rather paranoid.”